Over the past few years, most organizations have made real progress in detection. Telemetry is broader, signals are better correlated, and MDR has helped cut through a lot of the noise.
But the response hasn’t kept up.
In most environments, it still depends on who’s available, what time it is, and how quickly someone can make a decision. That delay, especially after hours and weekends, is where attackers gain ground. Not because they weren’t detected, but because nothing stopped them in time.
Introducing Deepwatch Active Response
This is exactly where Active Response comes in. Today, we’re pleased to announce Deepwatch Active Response for Identity and Endpoint, extending Deepwatch’s Precision MDR capabilities beyond detection into controlled, real-time containment across the modern attack surface.
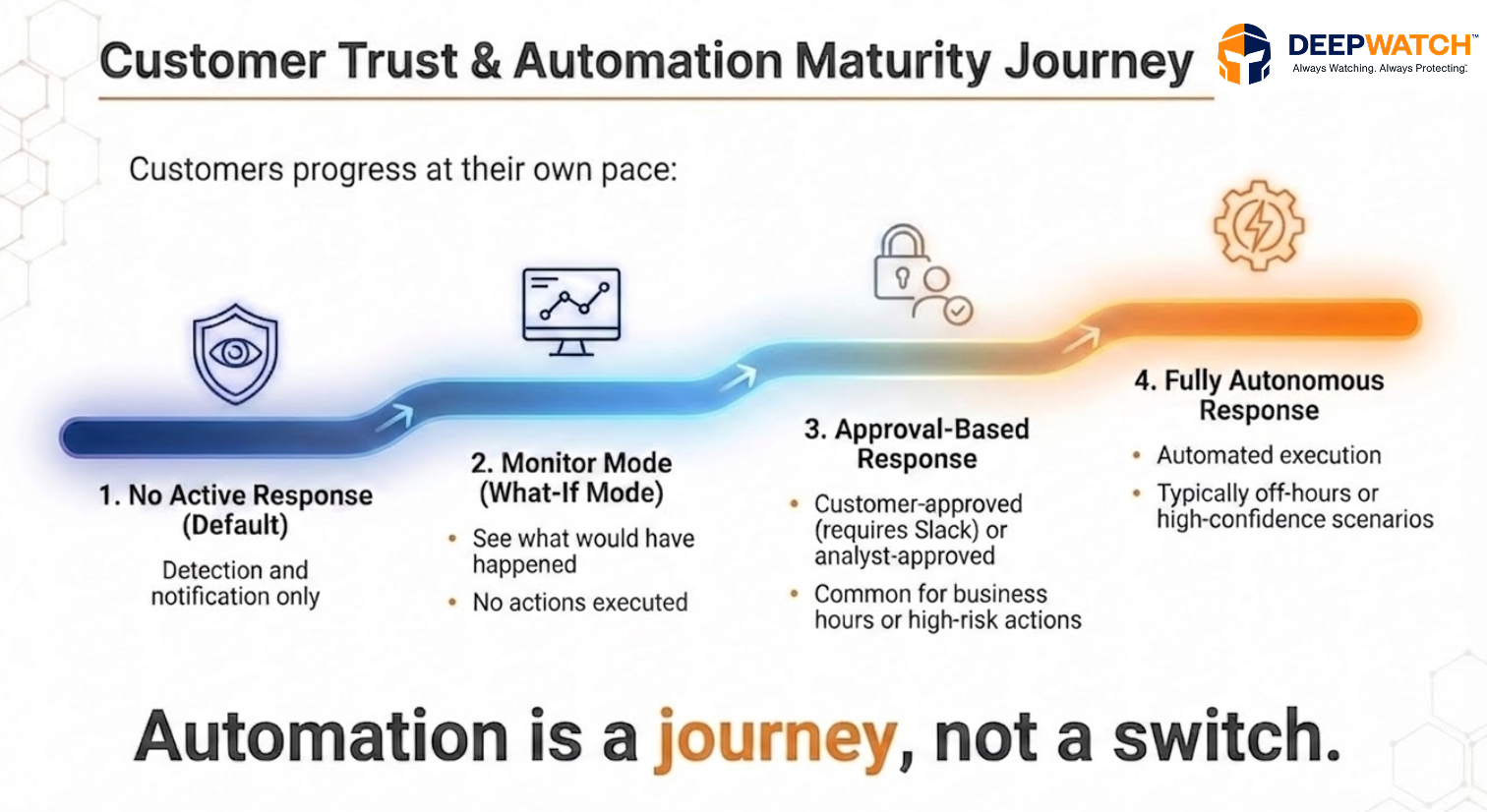
Active Response for Identity and Endpoint is designed to balance speed, safety, and trust. It does this through four core principles:
- Opt-in by design – no changes to your environment by default.
- Risk-aware automation – responses align to your tolerance and intent.
- Service-led execution – guided by Deepwatch analysts, not generic playbooks.
- Focused scope – built around high-confidence identity and endpoint detections. This ensures response actions are intentional, predictable, and auditable.
A Note from the Product Team:
| When we designed Active Response, our goal was clear: visibility only provides true value when it’s paired with predictable, reliable actions. We refused to build a ‘black box’ because we know our customers can’t afford to lose trust in their own network. |
Putting Intent into Action
At the heart of Active Response is the Response Intent Matrix, a collaborative framework that puts control firmly in the hands of the customer. It defines which detections should trigger a response, what actions are appropriate, the conditions under which they apply, and how those actions are executed, whether monitored, approved, or fully automated.
This approach ensures the response is not one-size-fits-all. For example: You might be comfortable with us killing a malicious process on a standard workstation automatically on a Saturday, but for your C-Suite? We’ll monitor and alert your team first, no matter the hour.
| Entity Targets | Conditions | Execution Mode | Action |
| Workstations | Group: Employee_Laptops Risk Score: Medium | Business Hours: Analyst Approved Off-Hours: Autonomous Weekends: Autonomous | – Process Kill – Host Isolation |
| Execs | Group: ELT Risk Score: High | All Times: Monitor Only | None (Monitor Mode – Observe Only) |
| Employees | Group: Employees Risk Score: Medium | Business Hours: Analyst Approved Off-Hours: Autonomous Weekends: Autonomous | – Password Reset – Account Disable – Session Revocation |
Conclusion
Beyond operational gains, the real shift is in how the SOC operates, moving from reacting to alerts to acting decisively in real time. Here’s the reality: detection is only half the battle. If you aren’t responding in seconds, you’ve already lost, and Active Response is what makes that possible.
If you’re looking to see how this works in practice, the next step is simple. You can request a demo to experience how Active Response operates within real-world workflows.
↑
Share