Key Points:
- Active exploitation has been observed by Rapid7 for a critical vulnerability in WSO2 API Manager, Identity Server (including Analytics and Key Manager), and Enterprise Integrator after proof-of-concept exploit code was made publicly available on GitHub and shared on Twitter.
- The vulnerability, tracked as CVE-2022-29464, allows remote code execution due to an unauthenticated, unrestricted file upload vulnerability. These products are normally internet-facing, which give threat actors direct access to attempt exploitation.
- Deepwatch Threat Intel Team assesses with high confidence that threat actors will use the publicly available exploit code to facilitate their attacks. It is likely that threat actors will abuse the vulnerability as an opportunity to gain initial access into an organization for further intrusion activities, like the deployment of ransomware, state-sponsored cyber espionage, coin miners, backdoors, and bots. To mitigate the risk associated with this vulnerability, the Deepwatch Threat Intel Team recommends customers follow WSO2’s mitigation steps in their advisory.
Overview
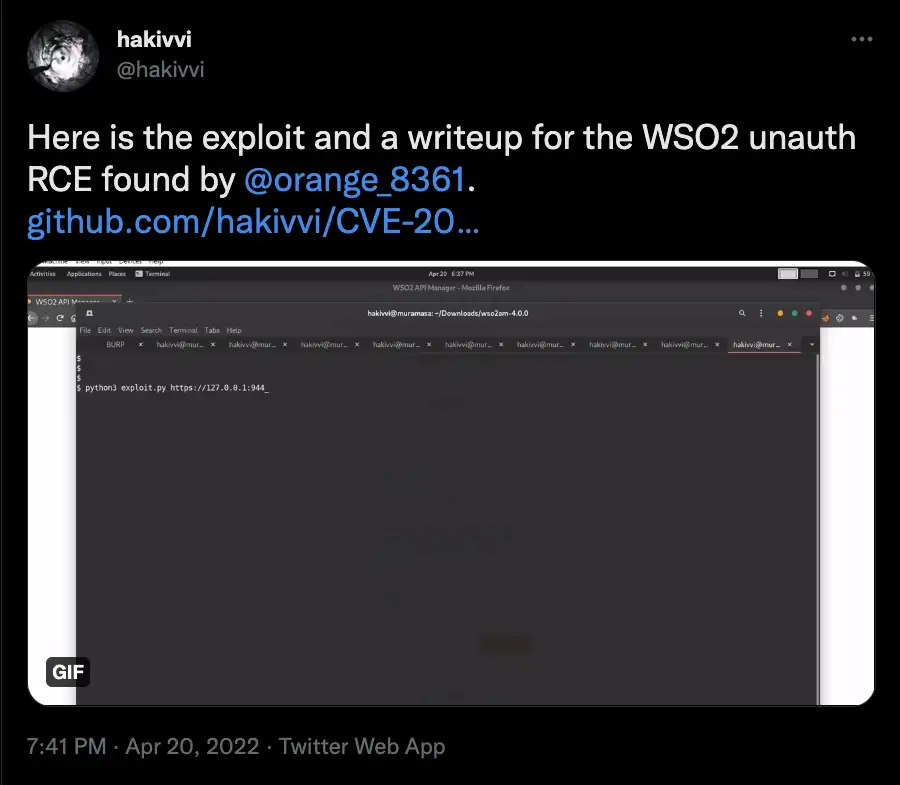
Rapid7 has observed threat actors exploiting an unauthenticated, unrestricted file upload vulnerability, tracked as CVE-2022-29464, in WSO2 products after proof-of-concept (PoC) exploit code was publicly disclosed by security researcher hakivvi on April 20.
Vulnerability Details
According to WSO2’s security advisory, the vulnerability exists in certain WSO2 products that allows remote code execution (RCE) due to an unauthenticated unrestricted file upload vulnerability. The vulnerability has been rated a CVSS score of 9.8 (CVSS:3.1/AV:N/AC:L/PR:N/UI:N/S:U/C:H/I:H/A:H).
Affected Products
According to WSO2, the products listed below are affected by CVE-2022-29464:
- WSO2 API Manager 2.2.0 and above
- WSO2 Identity Server 5.2.0 and above
- WSO2 Identity Server Analytics 5.4.0, 5.4.1, 5.5.0, 5.6.0
- WSO2 Identity Server as Key Manager 5.3.0 and above
- WSO2 Enterprise Integrator 6.2.0 and above
Note: According to WSO2, “the vulnerability may affect older product versions that are in extended and discontinued statuses as well.”
Proof-of-Concept Exploit Code Released
On April 20, a security researcher released PoC exploit code on GitHub and shared it on Twitter. The exploit uploads a Java file to /fileupload/toolsAny on the WSO2 product’s webserver. This vulnerability is not restricted to just Java files, as one security researcher has demonstrated exploitation with .war file types.
Active Exploitation
In the days following the first PoC exploit code being publicly available, Rapid7 stated that they have observed active exploitation of the vulnerability and that threat actors “appear to be staying close to the original proof-of-concept exploit and are dropping web shells and coin miners on exploited targets. Victim systems include both Windows and Linux installations of the aforementioned WSO2 products”.
What You Need to Do
Deepwatch Threat Intel Team recommends verifying with your IT management team that the affected products are deployed in your environment, and if so, following WSO2’s mitigation steps in their advisory. Additionally, the original PoC uploads a .jsp file to /fileupload/toolsAny and drops a web shell to /authenticationendpoint/, so auditing logs for this activity could indicate possible exploitation.
Deepwatch Threat Intel Outlook:
Deepwatch Threat Intel Team assesses with high confidence that threat actors will use the publicly available exploit code to facilitate their attacks. It is likely that threat actors will abuse the vulnerability as an opportunity to gain initial access into an organization for further intrusion activities, like the deployment of ransomware, state-sponsored cyber espionage, coin miners, backdoors, and bots. To mitigate the risk associated with this vulnerability, the Deepwatch Threat Intel Team recommends customers follow WSO2’s mitigation steps in their advisory.
Sources
https://www.rapid7.com/blog/post/2022/04/22/opportunistic-exploitation-of-wso2-cve-2022-29464/
https://cve.mitre.org/cgi-bin/cvename.cgi?name=CVE-2022-29464
https://twitter.com/hakivvi/status/1516925149597122572?s=20&t=KNARBGPzVT6nMCOdZklyYw
https://docs.wso2.com/display/Security/Security+Advisory+WSO2-2021-1738
https://twitter.com/wvuuuuuuuuuuuuu/status/1517433974003576833?s=20&t=xcKuDbSZX0ewsdKUIXZ7YA
Share